|
Today, we’re announcing the general availability of AWS IAM Identity Center support for multiple regions to enable access to your AWS account and use of managed applications in additional AWS regions.
With this feature, you can replicate your worker identities, permission sets, and other metadata in your organization’s IAM Identity Center instance connected to an external identity provider (IdP), such as Microsoft Entra ID and Okta, from your current primary realm to other realms for better AWS account access resiliency.
You can also deploy AWS-managed applications in your preferred regions, close to application users and datasets for a better user experience or to meet data placement requirements. Your applications deployed in other regions access replicated workforce identities locally for optimal performance and reliability.
When you replicate your workforce identities to another region, your workforce gets an active AWS Access Portal endpoint in that region. This means that in the unlikely event of an IAM Identity Center outage in its primary region, your workers can still access their AWS accounts through the AWS Access Portal in another region using the permissions already established. You can continue to manage IAM Identity Center configurations from the primary realm while maintaining centralized control.
Enable IAM Identity Center in multiple realms
To get started, you should confirm that the AWS-managed applications you’re currently using support a customer-managed AWS Key Management Service (AWS KMS) key enabled in the AWS Identity Center. When we introduced this feature in October 2025, Seb recommended using AWS KMS keys for multiple regions unless your company’s policy restricts you to single region keys. Multi-region keys provide consistent key material across regions while maintaining an independent key infrastructure in each region.
Before replicating IAM Identity Center to another realm, you must first replicate the customer-managed AWS KMS key to that realm and configure the replicated key with the permissions required for IAM Identity Center operations. For instructions on creating replica keys for multiple regions, see Creating Replica Keys for Multiple Regions in the AWS KMS Developer Guide.
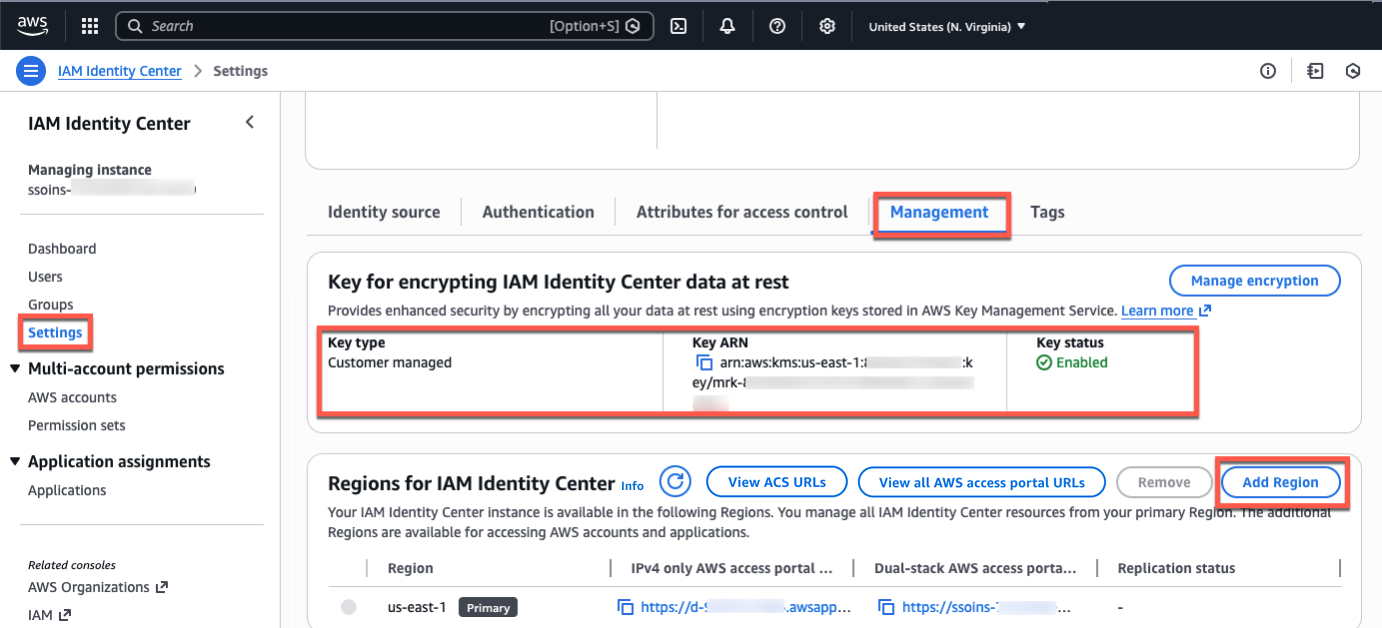
Go to the IAM Identity Center console in the primary region, for example USA East (N. Virginia), select Settings in the left navigation pane and select Management table Confirm that your configured encryption key is a customer-managed AWS KMS key for multiple regions. Select to add more areas Add region.
In the list of available realms, you can select additional realms for IAM Identity Center replication. When choosing the next area, consider your intended use cases, such as data compliance or user experience.
If you want to run AWS-managed applications that access datasets restricted to a specific region for compliance reasons, select the region where the datasets are located. If you plan to use another Region to deploy AWS applications, verify that the desired applications support the selected region and deployment in other regions.
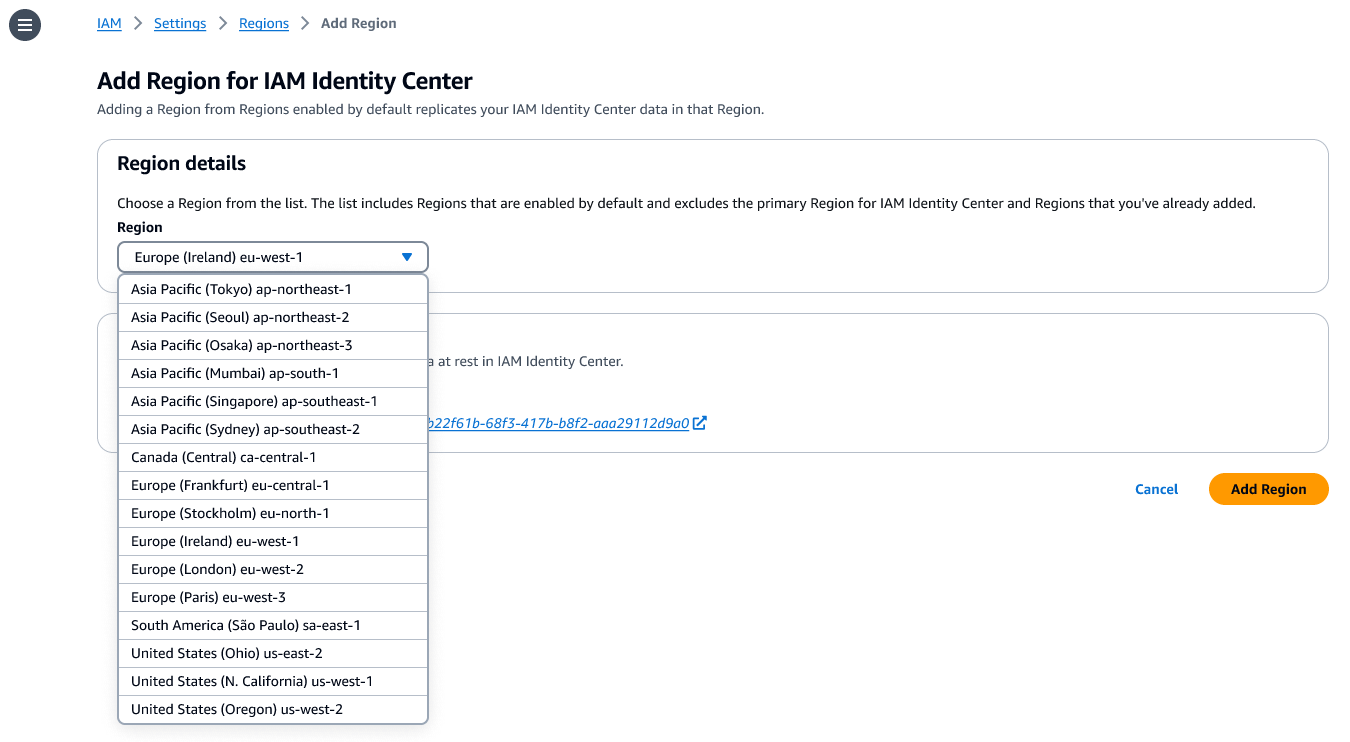
Choose Add region. This will start the initial replication, the duration of which depends on the size of your Identity Center instance.
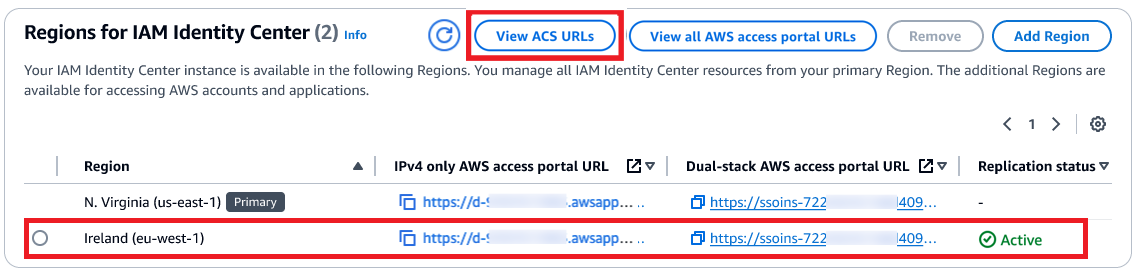
After replication is complete, your users will be able to access their AWS accounts and applications in this new region. When you choose View ACS URLsyou can view SAML information, such as the Assertion Consumer Service (ACS) URL, about primary and other realms.
How your employees can use the next region
AWS Identity Center supports SAML single sign-on with external IdPs such as Microsoft Entra ID and Okta. After authentication in the IdP, the user is redirected to the AWS access portal. To enable user redirection to the AWS access portal in the newly added realm, you must add the ACS URL of the additional realm to the IdP configuration.
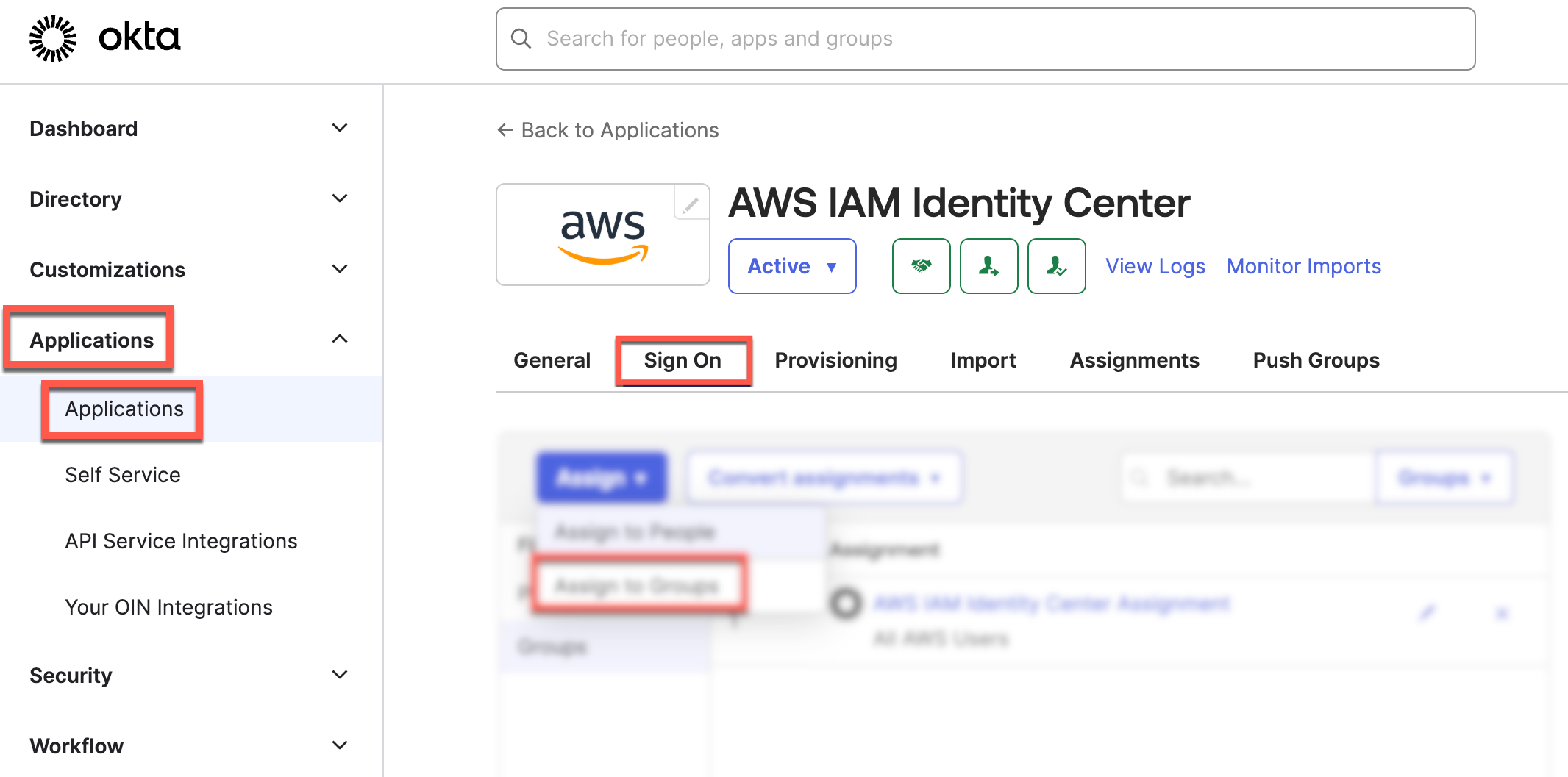
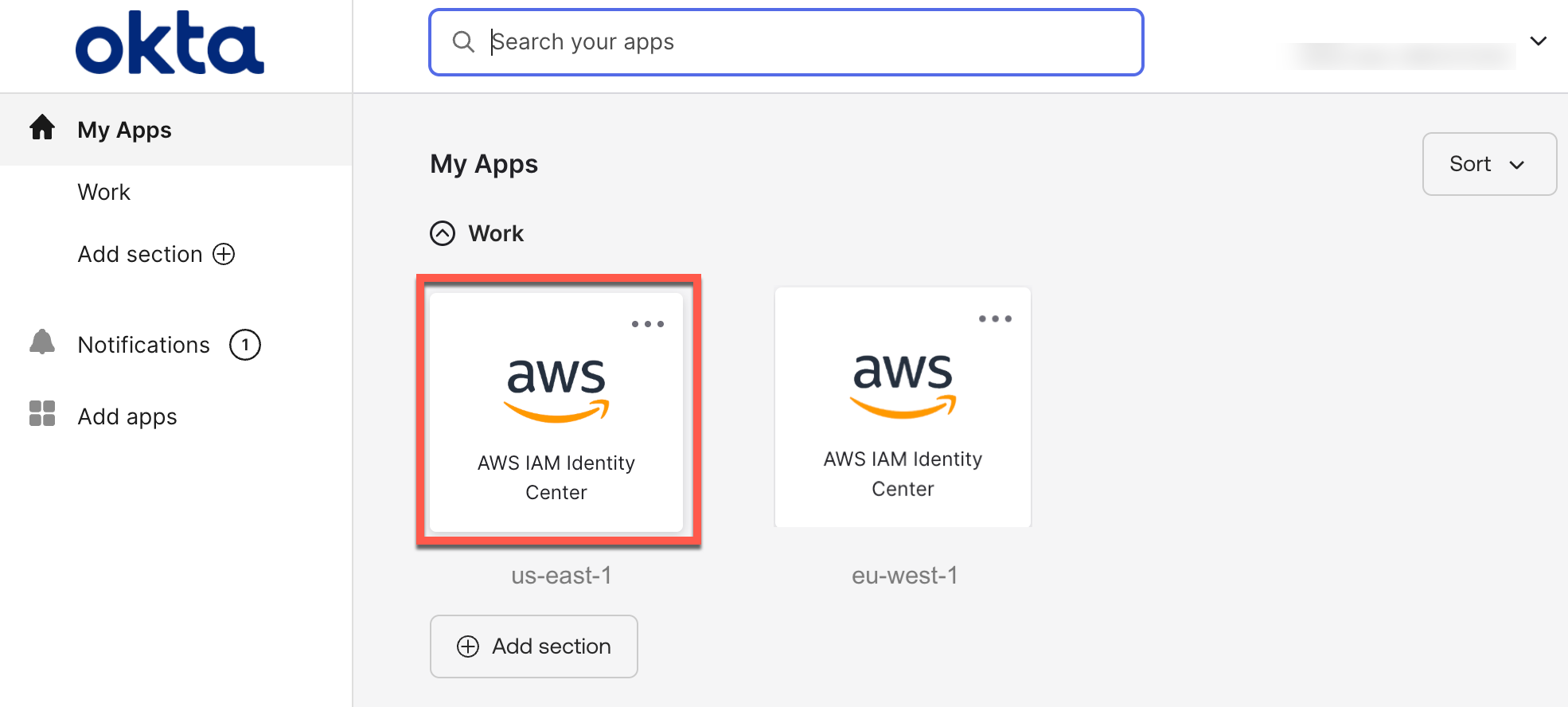
The following screenshots show how to do this in the Okta admin console:
You can then create a bookmark application in your identity provider so users can discover another area. This bookmark app works like a browser bookmark and contains only the URL of the AWS access portal in the next area.
You can also deploy AWS managed applications to other regions using existing deployment workflows. Your users can access applications or accounts using existing access methods, such as the AWS Access Portal, an application link, or through the AWS Command Line Interface (AWS CLI).
To learn more about which AWS-managed applications support deployment in other areas, visit the IAM Identity Center User Guide.
Things you should know
Here are the key considerations you should know about this feature:
- Consideration – To take advantage of this feature at startup, you must be using an IAM Identity Center organizational instance connected to an external IdP. Primary and other regions must also be enabled by default in the AWS account. IAM Identity Center account instances and the other two identity sources (Microsoft Active Directory and the IAM Identity Center directory) are currently not supported.
- Operation – The primary realm remains the central location for managing worker identities, account access permissions, external identity provider, and other configurations. You can use the IAM Identity Center console in other areas with a limited feature set. Most operations are read-only, except for application management and revoking the user session.
- Tracking – All workforce actions are broadcast in AWS CloudTrail in the region where the action was taken. This feature improves the continuity of account access. You can set up broken glass access for privileged users to access AWS if the external IdP has a service outage.
Now available
AWS Multi-Region Support IAM Identity Center is now available in the 17 default enabled commercial AWS regions. See AWS Capabilities by Region for regional availability and future plans. You can use this feature at no additional cost. Standard AWS KMS fees apply for storage and use of customer-managed keys.
Try it in the AWS Identity Center console. To learn more, visit the IAM Identity Center User Guide and submit feedback on AWS re:Post for Identity Center or through your usual AWS support contacts.
— Channy